Wannacry Patch Manual Download
MS17-010: How to install security update (WannaCry) To install MS17-010 security update, we need to download the corresponding patch from Microsoft update catalog server depending upon the operating system. Windows XP SP3. Open Microsoft Update Catalog Server's URL then search for KB4012598. May 04, 2018 Tech support scams are an industry-wide issue where scammers trick you into paying for unnecessary technical support services. You can help protect yourself from scammers by verifying that the contact is a Microsoft Agent or Microsoft Employee and that the phone number is an official Microsoft global customer service number.
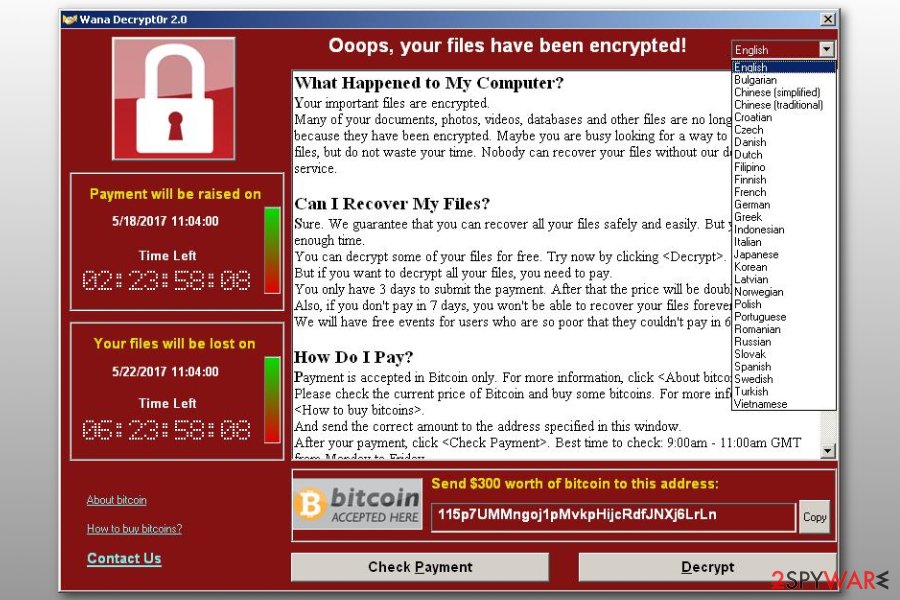
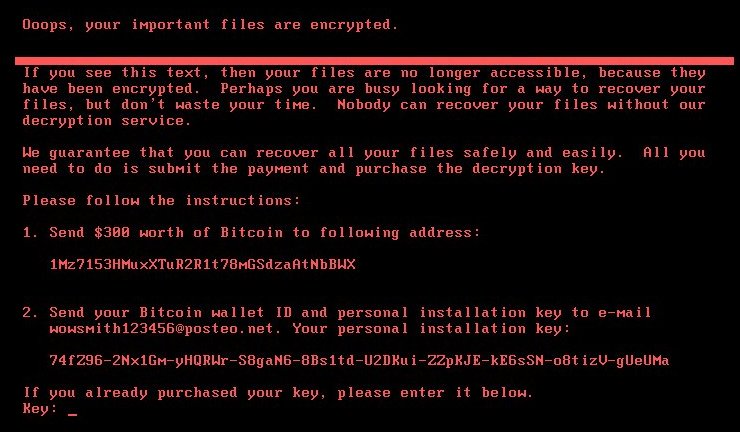
The world is now facing the biggest cyberattack known as the WannaCry ransomware. The WannaCry Ransomware has affected more than 2,00,000 computers worldwide. The WannaCry ransomware targets the computers running the outdated Microsoft Windows operating systems like the Windows XP, Windows Server 2003, Windows 7/8. After getting in a computer this malware first tries to connect to a domain name which is hard coded in its source code. If the domain name is not found then it encrypts the entire hard drive and asks for ransom from the victims. This domain name actually acted as a kill switch and was discovered and registered by- May 21, 2017 WannaCry Ransomware Decryption Tool Released Free; Unlock Files Without Paying Ransom If your PC has been infected by WannaCry – the ransomware that wreaked havoc across the world last Friday.
- Sep 10, 2012 Download Update for Windows Server 2008 R2 x64 Edition (KB2741355) from Official Microsoft Download Center. Update for Windows Server 2008 R2 x64 Edition (KB2741355) Important! Selecting a language below will dynamically change the complete page content to that language. Click the Download button and then do one of the following.
Before the WannaCry cyberattack, Microsoft patched the vulnerability in its Windows 10 OS by releasing a critical software update known as MS17-010 in March 2017. At that time MS17-010 was not released for other Windows OS'. After the WannaCry ransomware attack, Microsoft aggressively released security updates for all its Windows operating systems including the Windows XP whose support was ended by Microsoft in April 2014.
The MS17-010 is your computer's first defense to prevent the WannaCry ransomware attack. If you haven't installed this security update then find this post useful as we are going to teach you how to install this patch either via Windows update or standalone update package. Read upgrade to Windows 10 for free.

- Download the MS17-010 (KB4012212) update package 32-bit | 64-bit
- Download the update package according to the operating system you are using, that is 32-bit or 64-bit.
- After downloading the update package, double click it to open an install.
- Installation may take few minutes.
- Restart your computer after installation.
- To verify the update go to 'Control panel>Windows update'. Click 'Installed Updates' and look for 'KB4012212'. If it is listed then MS17-010 has been successfully installed.
Now after installing the security patch update make sure to scan your PC with a good antivirus. We suggest you buy Avast Internet Security 2017 because it detects, blocks and remove all malware strains of WannaCry ransomware including WNCRY, WCRY and Wana Decryptor 2.0. If you are still using Windows defender then I must tell you that Windows defender is unable to defend your computer against WannaCry. You can install Avast Internet Security 2017 which comes with a 30-day trial. Avast is the only antivirus which provides the highest security against WannaCry and DoublePulsar. Below you can find a screenshot in which Avast antivirus blocked the WannaCry virus.
Download Avast Internet Security 2017
If you have any questions then you can ask via comments. If you liked the article then take two minutes to share it.
You May Also Read
Get Blog Updates Via Email Subscribe Now
Please check your email for the verification link. Click on the verification link to start your email newsletter subscription.
 I needed to ensure we had this patch on hundreds of servers that are pretty much unmanaged. I've used various tools in the past but had to figure out how to do it to my windows 8.1 and 2012R2 hosts. This applies to any manual patch really.
I needed to ensure we had this patch on hundreds of servers that are pretty much unmanaged. I've used various tools in the past but had to figure out how to do it to my windows 8.1 and 2012R2 hosts. This applies to any manual patch really. First, I used psexec from the sysinternal tools at Microsoft https://technet.microsoft.com/en-us/sysinternals/bb897553.aspx.
I needed a way to get the update onto the machines without needing credentials to access a network share. I figured out how to use powershell to copy the file from a web server I've already setup.
I copied the update msu file to the webserver with a simpler name and renamed it as a .zip file to eliminate issues with file transfer through the web server. IIS will block the file unless you have a content type configured for the extension msu.
I created a simple text file with the IP addresses of all the hosts I wanted to patch. one per line. e.g.
10.10.10.2
Using the powershell command Invoke-WebRequest is like using wget. Just define the output file and specify the web url of the file.
e.g. powershell Invoke-WebRequest -OutFile c:tempupdate.msu http://mywebserver/update.zip
With psexec, you should specify the full path to the file. Finding powershell path is simple. Just type where powershell from a command line.
The psexec command example for a list of hosts
psexec @buildshosts.txt -s -u username -p password C:WindowsSystem32WindowsPowerShellv1.0powershell.exe Invoke-WebRequest -OutFile c:tempupdate.msu http://mywebserver/update.zip
Alternatively you can just issue it directly to a host
Wannacry Patch Windows 7
psexec 10.10.10.1 -s -u username -p password C:WindowsSystem32WindowsPowerShellv1.0powershell.exe Invoke-WebRequest -OutFile c:tempupdate.msu http://mywebserver/update.zip
Now that the patch was on the host, I used psexec to apply it using the standalone wusa stand alone tool. Since I know it is in the default path c:windowssystem32, I didn't bother to specify the path.
I included the /quiet and /forcerestart options to silently install and then reboot.
Wannacry Patch Kb
psexec @hosts.txt -s -u username -p password wusa c:tempupdate.msu /quiet /forcerestart
The patch update tool exits with code 1641 if the application and reboot was successful.
The process is done serially so, it takes a while to iterate through a large number of hosts.
Using powershell to do a web download is really slow, so it takes several minutes to download the 200K rollup.
There is a chance powershell is old and doesn't support the Invoke-WebRequest option.